If you’re using a strong password, brute-forcing is a very inefficient way of breaking into your WordPress account, and if it is really strong, dictionary attacks won’t help much either. However, there are are other, easier, ways for a mischievous person to get their hands on your login credentials e.g. with phishing, keyloggers or a MITM attack. By using a two-factor solution, you will increase your login security by an order of magnitude.
Enabling two-factor authentication means that to get authenticated you need to provide something you know (your password) and something you have (like your smartphone or a hardware key generator).
Implementations
There is a group of people working to get two factor authentication built right into WordPress. It looks very promising, but until they are release-ready, I suggest you look into one of the following implementations. They will continue to work even if WordPress core gets two factor authentication built-in.
Duo
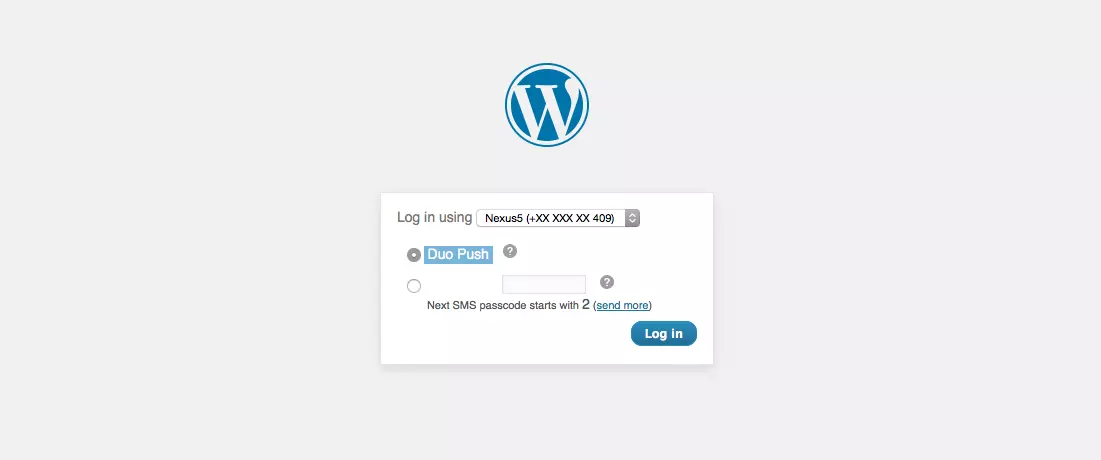
A two factor solution used in many enterprise environments, but it is free for up to 10 users. If you lose your phone, you can have backup codes sent to you by SMS.
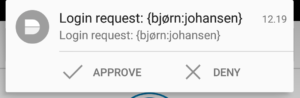
This is by far the easiest to use mobile based two factor authentication solution I’ve ever tried. After you have entered correct user credentials, you are presented with two options: Duo Push or codes from a SMS text message. The first one will send a push request to your phone and you can approve the login with a single tap directly from the push notification. Brilliant!
The mobile app also works with all other services that use TOTP (same as Google Authenticator).
Their web site: https://www.duosecurity.com/
The WordPress plugin: https://wordpress.org/plugins/duo-wordpress/
YubiKey
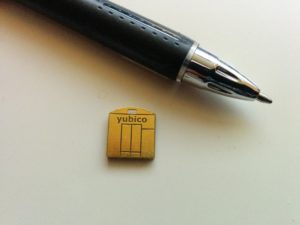
A popular hardware solution in many enterprise environments, the YubiKey is a hardware USB dongle that generates a one time use code on request. Actually, it is recognised by your computer as a keyboard. When you tap the dongle it will input the keycode wherever your cursor is focused.
The physical YubiKey comes in two flavours, one in the same size as normal USB thumbdrives and the YubiKey Nano which can stay in a USB port at all times, just standing a few millimeters out of the port.
There is no official WordPress plugin from YubiKey, but on their web site they are referring to the plugin by Henrik Schack.
Their web site: https://www.yubico.com/
The WordPress plugin: https://wordpress.org/plugins/yubikey-plugin/

Rublon
I hear very good things about Rublon. It is pretty much just as easy to use as Duo. To log in, you simply click a link in your email or scan a code on the web page. This means you don’t even need your phone (but please use 2FA for your email account as well).
Rublon is free for 1 account per website.
The WordPress plugin: https://wordpress.org/plugins/rublon/
Clef
I haven’t tested Clef yet, but a while ago I noticed that several people seemed enthusiastic about it.
Their web site: https://getclef.com/
The WordPress plugin: https://wordpress.org/plugins/wpclef/
Authy
Authy is another solution that people seem to like a lot, but I haven’t got around to test yet.
Their web site: https://www.authy.com/
The WordPress plugin: https://wordpress.org/plugins/authy-two-factor-authentication/
Google Authenticator
There are actually two plugins who have implemented two factor authentication with Google Authenticator (neither is official). It’s been a long time since I’ve tried either, but I don’t recommend them: If you reinstall your phone, you have no backup means of logging in and will have to disable the plugin – by having another admin do so for you, or using SSH/SFTP to rename the plugin folder.
https://wordpress.org/plugins/google-authenticator/
https://wordpress.org/plugins/wp-google-authenticator/
Remember: Use HTTPS
Please remember that if you don’t use HTTPS to encrypt the connection between you and WordPress, it is still possible for an attacker to hijack your session.
What’s your experience?
If you’re using two factor authentication for WordPress, please share your experience in the comments – especially if you’re using a method I don’t have any experience with yet :-)
Interesting logic behind not using Google authenticator. I tend to use it just because I already have it installed, and it works.
Also having to scroll a long list of accounts to find those 6 digits, and then typing them in manually, is too much hassle when there are easier ways to do it :-)
I use Duo Security on my private site and on a multisite. The ease of use is the main factor for selecting Duo. So far I haven’t had any support issues on the multisite. The users, ca 50 editors, are non-techies.
Hey,
nice comparison between this tools.
But, wouldn’t it be better to use a .htaccess file as “two factor authentication” ?
When your website is under DDOS, and you use one of this tools , every request on your login page will trigger the whole php-stack.
With a ,htaccess any DDOS will be handled by the web server and not by the php stack, so it will be “cheaper”.
OK, you have to authenticate twice …
Best,
Martin
Thank you.
What do you suggest I use the .htaccess file for?
If you’re thinking about protecting wp-admin with HTTP auth, that’s not two factor auth. It would be two summand auth and really a useless summand in terms of authentication protection, since it would be just as easy to pick up the added authentication credentials as your WP username/password.
For handling a DDoS to a particular URL – like wp-admin – it helps, just as restricting access to WordPress login by IP address does. Except the latter also protects against unauthorized access on the IP level (that will actually be considered a second factor).
If you by “using .htaccess” mean a client certificate, that will most definitely be considered a second factor. It’s on my list of subjects I will write about.
im actually use DUO
and always send me a push notification, it fantastic, other great 2fa, is LATCH
ans its very simple to configure
but in the personal i love duo :D
https://latch.elevenpaths.com/
I would recommend a WordPress security plugin that has inbuilt option to serve the TFA rather than go for a separate plugin just for TFA!
I strongly disagree. It’s generally better to have each component just doing one thing (and doing that one thing well).
Will you please elaborate on why you would recommend a general security plugin instead?
I have tried authy and clef and I have to say clef is very easy to use and integrate. Authy requires either a token or uses a button similar to Duo which makes it very interesting. Plus their dashboard is fully featured and well presented.
Clef’s dashboard is definitely too simplistic and doesn’t offer a lot of options. But the login process is fun and easy.
But I feel most of these solutions lack a few important features,
-Support SMS or phone calls
-But can’t rely stickly on phone app all the time
you might lose your phone
you might not have a phone signal but still have a internet connection (not WiFi)
-Need to be able to fallback to other options in some cases, like tokens sent by emails
-Need to have the option to setup FIDO biometrics authentication
-Need to support Touch Id or others
-Need to control session duration
-Well documented and easy integration
I am still trying to find what I need and there’s a lot of solutions out there. But I feel like the best solutions are way too expensive.
I really like the new 2FA feature plugin. It was a breeze to create a new SMS-based auth method, and you can activate multiple methods, so you can fallback to email, TOTP and others if you like.
I’ve used Clef and it was good but I’ve recently switched to LoginTC because of their Chrome App which simplifies the login process a lot.
https://www.logintc.com/docs/guides/chrome-app.html
1 vote for Duo
I use the Google Authenticator Plugin, one thing to note is that on old android phones, there is a glitch that makes the time sequence out of whack, and you don’t have enough time to log in. So If you are planning on implementing any of these plugins in your website, make sure you have a backup done before implementation, so you can recover your account if the plugin locks you out.
I have been using Authy but my question is how can we use SMS verification with this or any other plugin? I found another resource here https://www.cloudways.com/blog/two-factor-authentication-plugins-wordpress/ which uses various two factor authentication WordPress plugins but still not clear. Cheers!
There is an official feature project for WordPress called Two-Factor. The goal of this project is to be included in WordPress core.
It is really easy to extend this plugin with your own authentication methods, like SMS. I’ve created a couple in the past. Will see if I can find the sources again and make a post of it.
Awesome! That would be great. Thank you.